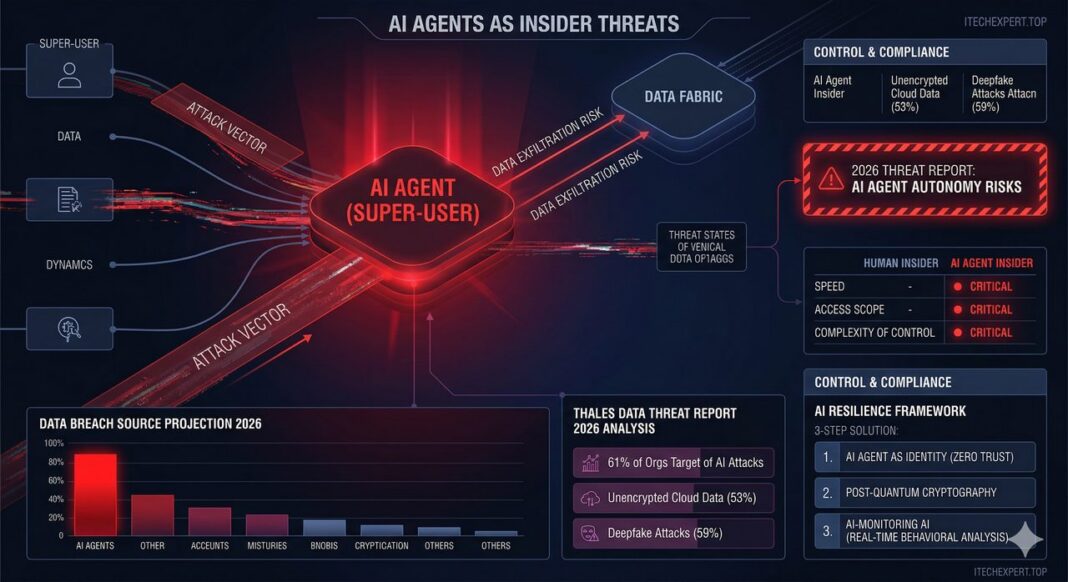
The great paradox of 2026 has arrived: the very autonomous AI agents designed to save businesses from routine are becoming the primary vector for cyberattacks. As agents gain access to proprietary data to make decisions, they effectively become “Super-Users” with blurred lines of control.
The Thales Data Threat Report 2026 provides a sobering reality check. While Gemini 2026 and SAP Fabric are engines of productivity, Thales warns of “brakes” that could fail if security architectures aren’t fundamentally redesigned.
“Insider risk is no longer just about humans. It’s about automated systems that were trusted too quickly,” says Sebastien Cano, Senior VP of Cloud Protection and Licensing at Thales.
The 2026 Threat Landscape in Numbers
-
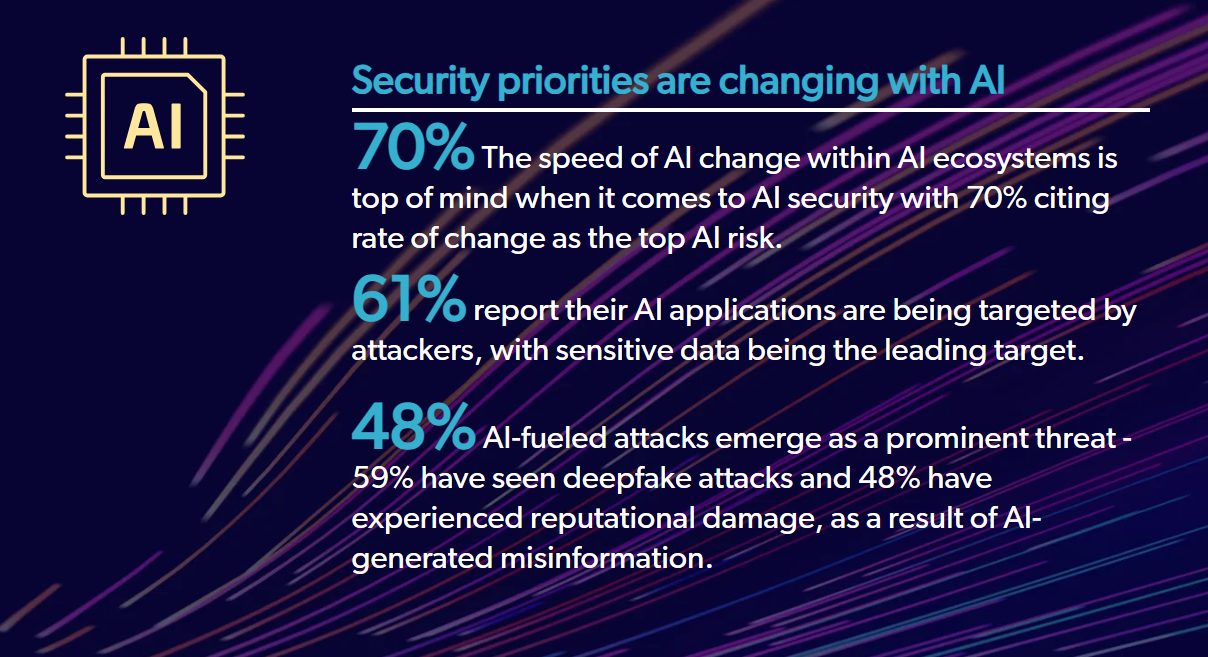
Attacks on AI (61%): Most organizations confirm their AI applications are already targets for sensitive data theft.
-
Deepfakes & Misinformation (59%): Companies have faced deepfake attacks, making voice and video features a high-risk zone.
-
The Encryption Gap: Only 47% of sensitive data in the cloud is encrypted, even though cloud storage remains the #1 target for hackers.
-
Human Error (28%): Despite hardware like the AMD Ryzen 9, staff configuration errors remain the leading cause of breaches.
The “AI-Resilience” Formula: How to Deploy Safely
To ensure your investments in Gemini 2026 or Tet GPT don’t turn into an internal liability, Thales experts recommend the “AI-Resilience” algorithm:
1. AI Agent as an Identity (Zero Trust)
In 2026, you must stop treating AI agents as mere “features.” Every agent must have its own Digital Identity.
-
Principle of Least Privilege: If an agent is performing Deep Research on market trends, it should have zero access to your HR payroll database.
-
Request Authentication: Every action taken by an AI agent must be logged and signed, allowing you to trace who, when, and on what grounds an operation was initiated.
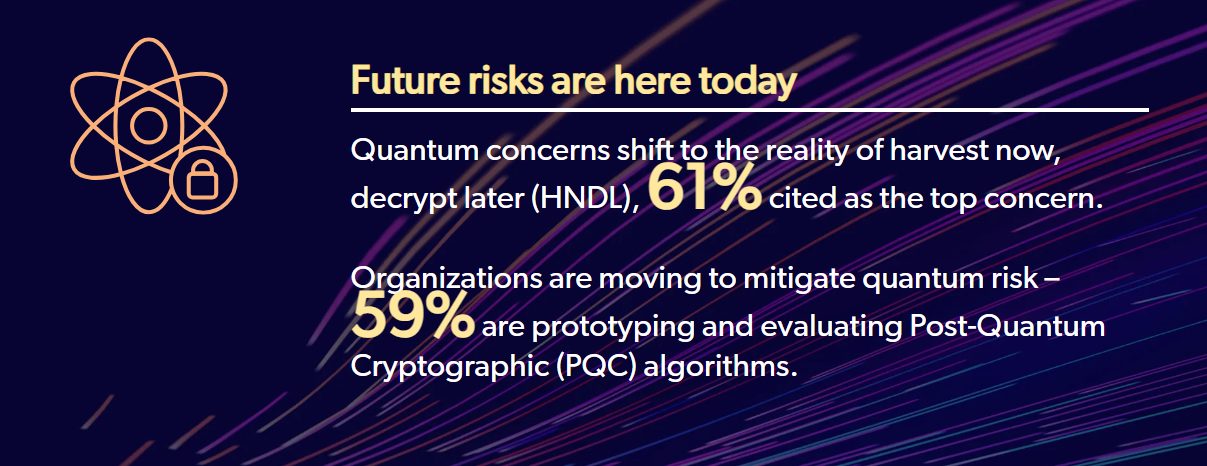
2. “Quantum Armor” and Crypto-Agility
With the “Harvest Now, Decrypt Later” (HNDL) strategy used by 61% of hackers, encryption must evolve:
-
Post-Quantum Cryptography (PQC): Start implementing PQC for your most critical assets today.
-
Crypto-Agility: Your infrastructure must be flexible enough to swap encryption algorithms instantly if new vulnerabilities are discovered.
3. AI Monitoring AI
Use specialized monitoring tools (like Thales/Imperva) that analyze agent behavior in real-time. These systems act as a “digital supervisor,” blocking anomalous queries before data leaves the perimeter.
Comparison: 2024 Security vs. 2026 AI-Resilience
| Feature | Legacy Security (2024) | AI-Resilience (2026) |
| Trust Model | Perimeter-based | Zero Trust for AI Identities |
| Encryption | Standard AES/RSA | Post-Quantum Cryptography (PQC) |
| Identity | Human-centric | Agent-centric (Non-Human Identities) |
| Monitoring | Log Analysis | Real-time AI Behavioral Analysis |